How to Govern MCP Access Across Teams, Customers, and Third-Party Integrations
MCP access governance requires scoped credentials, tool-level permissions, and audit trails. Learn how to govern MCP access across teams and integrations.
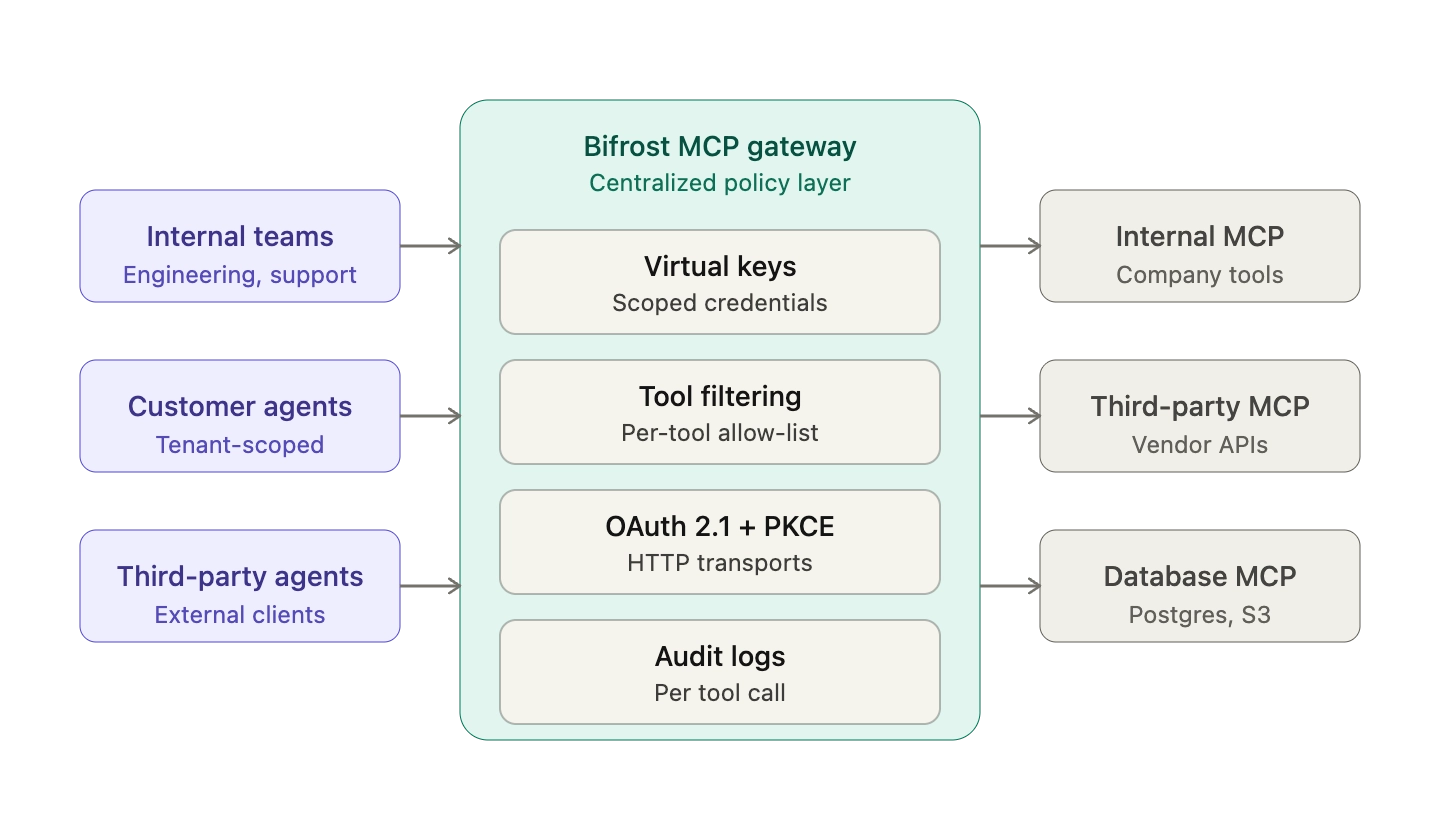
The Model Context Protocol (MCP) has become the de facto standard for connecting AI agents to external tools, data sources, and business systems. As production deployments grow, MCP access governance has emerged as the missing layer: the protocol defines how agents discover and invoke tools, but not who gets to invoke what, under which constraints, or how those actions are recorded. The gap matters most for engineering leaders wiring AI agents across multiple teams, customer-facing products, and third-party tool servers. Bifrost, the open-source AI gateway built by Maxim AI, was designed to close this gap with virtual keys, tool-level permissions, MCP Tool Groups, and audit logging at the gateway layer. This post outlines the practical patterns for governing MCP access in production and the controls every enterprise deployment should enforce.
What MCP Access Governance Means
MCP access governance is the set of controls that determines which AI agents, teams, customers, and applications can invoke which tools on which MCP servers, along with the accompanying audit, cost, and policy enforcement. It sits above the Model Context Protocol itself, adding identity, authorization, rate limiting, and observability that the protocol does not define natively.
The MCP authorization specification standardizes tool discovery, invocation, and (since the 2025-06-18 revision) an OAuth 2.1 authorization model for HTTP transports. What the specification does not prescribe is fine-grained, per-tool access control across a shared fleet of agents, teams, and customers. That responsibility lives in the deployment layer.
Why MCP Access Control Is Hard by Default
Three structural issues make MCP access control difficult without a dedicated gateway:
- No native per-tool authorization. OAuth 2.1 scopes authorize access to an MCP server, not to individual tools exposed by that server. Two agents holding identical tokens see the same tool surface.
- Tool metadata is an attack vector. Microsoft's developer team has documented "tool poisoning" attacks, where malicious instructions embedded in MCP tool descriptions are interpreted by the model as commands. Since tool descriptions are visible to the model but often not reviewed by humans, the attack class is hard to detect without runtime inspection.
- Third-party MCP servers are supply chain dependencies. Each external MCP server is code you did not write, processing inputs your agents generate, and returning outputs your model reads. Without a gateway, every client connects directly, every server defines its own auth, and no central policy applies.
These aren't theoretical risks. For enterprises running MCP in customer-facing products, the threat surface compounds with every added integration, and the current state of MCP authorization (OAuth 2.1, PKCE, and Dynamic Client Registration) only covers the entry point. Everything beyond that (which tool, which tenant, which budget) is left to the deployment.
Governing MCP Access Across Teams
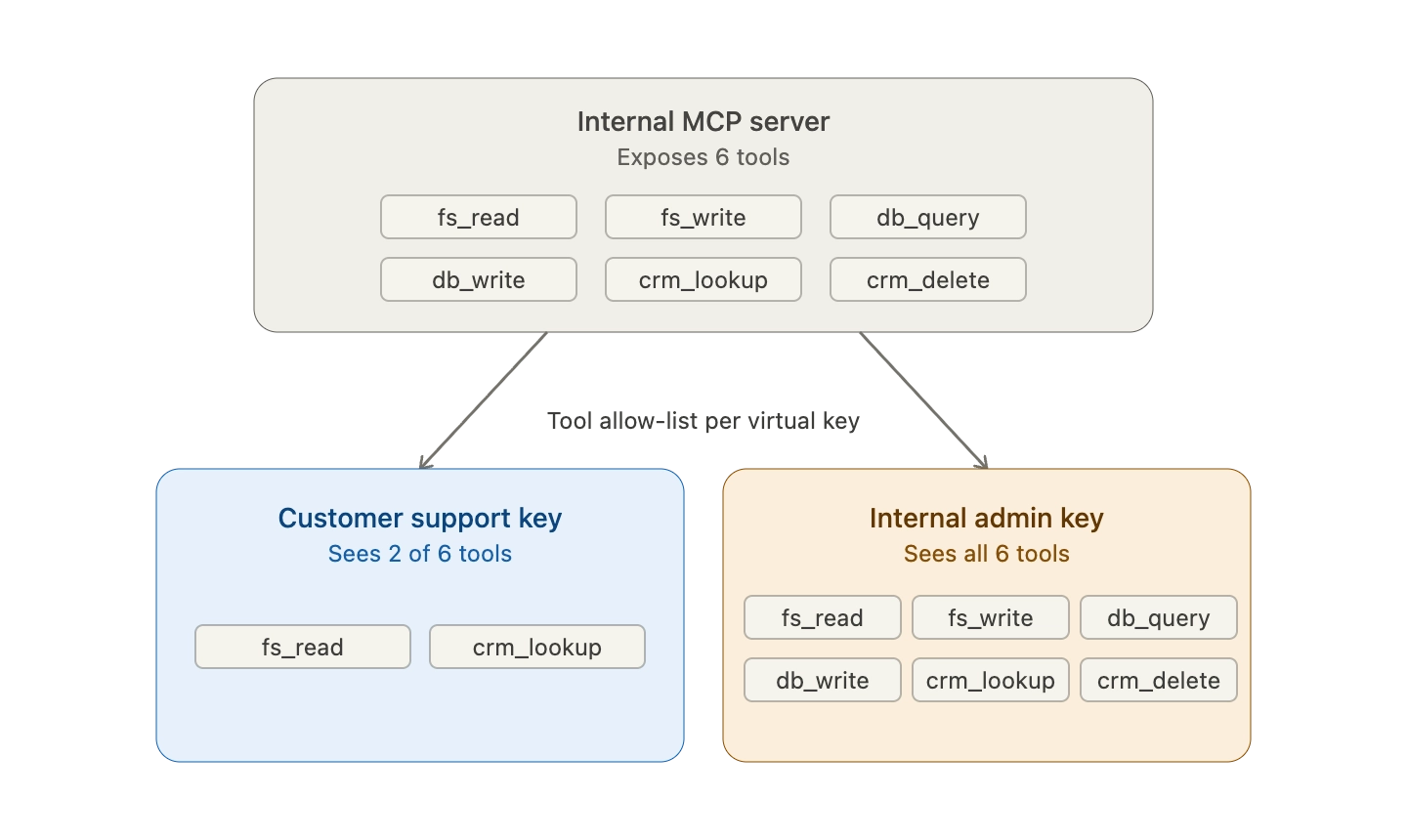
Multi-team MCP deployments need two controls working together:
- Scoped credentials per team. Each team receives a credential (a virtual key, an API token, or a scoped OAuth client) that authorizes only the tools relevant to its workflows. A customer-support agent's credential should not reach a database write tool exposed by the same MCP server.
- Tool-level, not server-level, allow-lists. Allow-lists at the server level are too coarse. A single MCP server often exposes read tools, write tools, and admin tools. The governance layer must let administrators approve
filesystem_readwhile excludingfilesystem_writefrom the same server.
Bifrost's virtual keys implement this pattern at the gateway layer. Each key carries a tool-level allow-list evaluated on every MCP request. The model never sees tool definitions outside its scope, which eliminates prompt-level workarounds entirely. For organizations with dozens of teams, MCP Tool Groups let administrators define named tool collections once and attach them to any combination of keys, teams, customers, or providers, with membership resolved at request time without per-call database lookups.
Governing MCP Access for Customer-Facing Agents
Customer-facing AI agents introduce multi-tenancy. Each customer must see an isolated tool surface, consume metered budget, and leave an auditable trace without affecting other tenants.
Three controls cover the critical cases:
- Per-customer credentials with tool and server restrictions scoped to the tenant's contracted features.
- Per-tenant budgets and rate limits that prevent a single customer from exhausting shared LLM or tool budgets.
- Per-tenant audit trails that let compliance teams reconstruct exactly which tools were invoked for a given customer within a given window.
Bifrost's governance model treats virtual keys as the primary tenant boundary. A credential issued to a customer integration inherits a specific tool allow-list, a spending budget, and independent rate limits. Every tool invocation is recorded as a first-class audit entry tied back to the originating key, which satisfies the compliance expectations that regulated industries apply to any system that can read or mutate their data.
Governing Third-Party MCP Integrations
Third-party MCP servers require a different risk model. You do not control the server, the tool definitions, or the upstream data. The governance layer becomes the only place where policy can be enforced reliably.
Four controls address this surface:
- OAuth 2.1 with PKCE and dynamic client registration for any HTTP-based third-party MCP server. The protocol now requires PKCE for public clients and supports dynamic registration per RFC 7591, which makes onboarding new servers safer without hardcoding client secrets.
- Tool filtering at the gateway so each consumer of the third-party server sees only a curated subset of its tools. Even if the third party exposes 50 tools, the agents behind the gateway see the 5 that are actually needed.
- Input and output inspection for tool arguments and responses, to catch tool poisoning and indirect prompt injection before they reach the model. Anthropic's engineering team has publicly documented how injecting every tool definition on every turn compounds both cost and attack surface.
- Immutable audit trails that record the full request and response chain, including the upstream server, the tool called, the arguments, and the virtual key that initiated the call.
Bifrost handles each of these at the gateway. OAuth 2.0 with PKCE, dynamic client registration, and automatic token refresh is built into the MCP connection layer. Tool filtering is evaluated per virtual key, and audit logs capture every tool invocation with full request and response context for SOC 2, GDPR, HIPAA, and ISO 27001 compliance.
Key Principles for Enterprise MCP Governance
Effective MCP access governance converges on a small set of principles regardless of which gateway implements them:
- Least privilege by default. No agent should see a tool it does not need. Start with an empty allow-list and expand deliberately.
- Centralized policy enforcement. One gateway, one policy surface. Per-client, per-team, and per-server policies should compose in a single place.
- Per-tool audit, not per-request. Every tool invocation is a first-class log entry with tool name, server, arguments, result, latency, and initiating credential.
- Cost visibility at the tool level. Token cost is only part of the picture. Tool execution often hits paid APIs with their own per-call pricing, which needs to be tracked alongside model spend.
- Short-lived, rotatable credentials. OAuth sessions, automatic token refresh, and revocation must be first-class operations.
- Content safety at the edge. Guardrails for input and output should sit at the gateway, not be bolted onto each agent individually.
How Bifrost Governs MCP Access End to End
Bifrost's MCP gateway centralizes the full control surface behind a single /mcp endpoint. Teams connect MCP servers once, and every agent (Claude Code, Cursor, internal agents, customer-facing agents) interacts with the gateway rather than directly with the server:
- Virtual keys scope credentials per consumer with per-tool allow-lists, budgets, and rate limits.
- MCP Tool Groups let administrators manage tool access across teams, customers, and providers at organization scale.
- OAuth 2.0 with PKCE, dynamic client registration, and automatic token refresh for third-party MCP servers.
- Federated authentication to transform existing enterprise APIs into MCP tools without changing upstream code, using identity providers like Okta and Entra (Azure AD).
- Tool-level audit logs, exportable to external log stores and SIEM systems, with content logging configurable per environment.
- Per-tool cost tracking alongside LLM token usage, giving engineering and finance teams a unified picture of agent-run economics.
- Code Mode for cost reduction on large tool inventories. Instead of injecting every tool definition into context on every request, the model reads lightweight Python stubs on demand and executes orchestration scripts in a sandboxed Starlark interpreter. Bifrost's controlled benchmarks show input tokens dropping by up to 92.8% across 16 MCP servers and 508 tools, with no loss in task accuracy.
The broader governance surface extends the same controls to LLM traffic: provider routing, fallbacks, rate limits, budget management, and unified audit across models and tools. Agent runs that span both an LLM provider and ten MCP tool calls leave a single, coherent trail instead of fragmenting across five separate dashboards.
Getting Started with MCP Access Governance
MCP is moving fast. New servers, new clients, and new attack techniques land every quarter. The organizations treating MCP access governance as a foundational layer rather than an afterthought are the ones shipping agents safely into regulated environments, customer-facing products, and cross-team deployments. Bifrost was built to be that layer, combining scoped access, tool-level permissions, audit logging, and cost visibility in a single open-source gateway. To see how MCP access governance works end to end on your own stack, book a demo with the Bifrost team.